How Do Universities Detect Essay Service Usage?
Universities use multiple sophisticated detection methods that work together to identify purchased work. No single method provides absolute proof, but combined evidence creates compelling cases against students.
Writing Style Analysis
Professors develop familiarity with each student’s writing through early assignments, discussion posts, and exam responses. They recognize individual patterns in vocabulary, sentence structure, voice, and argumentation style.
Sudden changes raise immediate suspicions. When a student who consistently makes subject-verb agreement errors suddenly submits flawless prose, professors notice. When basic writers suddenly produce sophisticated analysis rivaling graduate-level work, red flags appear.
Specific indicators professors identify:
- Vocabulary sophistication shifts: Advanced terminology never used in previous work.
- Sentence complexity changes: Dramatic increases in sentence length or structure variety.
- Voice inconsistencies: Different personality or perspective in writing.
- Argument quality jumps: Sudden analytical sophistication, unlike earlier submissions.
- Technical proficiency: Perfect grammar after consistent specific errors.
- Tone variations: Formal academic prose from students who write casually.
One professor explained: “I’ve graded hundreds of papers. When a C-student suddenly submits A+ work with complex theoretical frameworks they’ve never mentioned in class discussions, I know something’s wrong.”
Turnitin Authorship Investigation
Modern plagiarism detection extends far beyond text matching. Turnitin’s Authorship Investigation tool compares current submissions against students’ entire submission history across all courses.
The software analyzes multiple dimensions:
- Linguistic Analysis examines sentence complexity, word frequency, punctuation patterns, and vocabulary richness. Each writer has a unique “fingerprint” measurable through quantifiable features.
- Document Metadata reveals creation dates, author names, editing time, software versions, and modification history. Inconsistencies between claimed authorship and metadata create evidence of outsourcing.
- Stylometric Comparison uses machine learning to identify writing pattern changes. When current work differs significantly from established baseline patterns, the system flags submissions for investigation.
Research demonstrates effectiveness. In a study of 24 experienced markers evaluating 20 assignments (including six purchased from essay mills), detection accuracy increased from 48% without the tool to 59% with Authorship Investigation. While not perfect, this represents a 23% improvement in catching contract cheating.
- The tool generates prediction scores from 0 to 1.00:
0.57-0.76 (High Score): Likely contract cheating requiring investigation. - 0.77-1.00 (Critical Score): Highest flags and anomalies demanding immediate attention. Universities review these flagged submissions manually, combining software analysis with human judgment to build cases.
AI Detection Software
With 88% of university students now using generative AI for assessments, institutions deploy AI detection tools alongside traditional methods.
Turnitin’s AI writing detector identifies how much content likely came from AI versus human authors. The tool has processed hundreds of millions of student papers since launching in April 2023.
Detection data reveals:
- 11% of reviewed papers contained at least 20% AI-generated content.
- 3% consisted of at least 80% AI writing.
- 68% of teachers now use AI detection tools, up 30 percentage points year-over-year.
Although any legit essay writing service provides accurate AI reports. However, AI detection faces accuracy challenges. False positives occur, particularly for non-native English speakers or students with unique writing styles. Many institutions use detection results as investigation triggers rather than definitive proof.
Content and Source Verification
Professors examine essay content for revealing patterns:
Generic Arguments Essay mill papers present broad, universal analysis lacking course-specific details. They could apply to any similar course without referencing assigned readings, class discussions, or instructor-specific theories.
One professor noted: “When essays discuss general World War II facts without mentioning any materials from my syllabus or concepts we covered in class, I know the writer wasn’t in my course.”
Reference Anomalies signal purchased work:
- Citations to sources not in the course materials or accessible database.
- Suspicious reference formatting with identical blocks suggesting template reuse.
- Publication dates predating assignments or unavailable sources.
- AI-generated “hallucinated” citations to nonexistent articles.
- Reference styles inconsistent with the student’s previous submissions.
Professors increasingly verify citations by checking whether sources exist and support cited claims. AI-generated papers often include plausible-sounding but completely fabricated references.
Knowledge Gaps: Students unable to explain their arguments, defend positions, or discuss cited sources reveal they didn’t write the work. Many professors ask clarifying questions during office hours or require oral presentations defending written work.
Comparison with Other Performance
Professors cross-reference essay quality with other student performance indicators:
- Exam scores showing poor subject understanding despite excellent essays
- Class participation reveals shallow knowledge versus sophisticated written analysis
- Discussion posts using basic vocabulary, while essays employ advanced terminology
- In-class writing samples are dramatically different from take-home assignments
These inconsistencies create compelling evidence of outsourcing. Students who demonstrate C-level understanding on exams but submit A-level essays face justified suspicion.
Metadata and Technical Markers
Document properties sometimes expose essay mill origins:
- Contract numbers: Tracking codes in headers, footers, or properties (e.g., “CE- 1234-5678”)
- Author information: Document metadata showing different creator names
- Software versions: Programs students don’t own appearing in file properties
- Editing time: Unrealistic creation or editing durations for claimed authorship
- Time stamps: Creation dates conflicting with student access to assignment details
Essay mills occasionally leave these traces unintentionally. Savvy students remove metadata, but many don’t think to check.
Suspicious Plagiarism Patterns
Counterintuitively, extremely low plagiarism scores can indicate cheating. Many essay mills advertise “plagiarism-free” guarantees by running drafts through Turnitin and eliminating all matches.
The result: 0-2% similarity scores with awkward synonym substitution avoiding common field phrases. Natural academic writing typically shows 5-15% similarity from standard terminology, common phrases, and properly cited quotes.
Professors trained to recognize this pattern investigate further when similarity scores seem suspiciously perfect.
What Makes Your Essay Detectable?
Certain choices and circumstances dramatically increase detection likelihood. Understanding these factors helps students recognize what makes an essay service obvious.
Quality-Ability Discrepancy
The most glaring red flag is dramatic quality improvement inconsistent with demonstrated abilities. Professors notice when:
- Previous work shows specific recurring errors that suddenly disappear
- Vocabulary and complexity exceed what students display in class
- Theoretical sophistication appears nowhere else in student work
- Citation mastery emerges from students who previously struggled with basics
- Critical analysis depth far surpasses exam responses on identical topics
This discrepancy becomes especially obvious when exceptional essays accompany poor exam performance on the same material. Students who can’t explain basic concepts in tests but submit sophisticated written analysis raise obvious questions.
Writing Style Inconsistencies
Each writer has distinctive patterns:
- Sentence length preferences: Some favor short, punchy sentences; others write longer, complex ones
- Vocabulary choices: Word selection reveals education level and personal preference
- Paragraph structure: Organizational patterns remain relatively consistent
- Voice and tone: Formal versus conversational approaches
- Transitional phrases: Writers use their favorite connecting words repeatedly
When current submissions differ markedly from established patterns, professors investigate. This explains why Turnitin Authorship compares your work against your entire submission history.
Course-Specific Content Absence
Professors design assignments requiring engagement with specific materials:
- Assigned readings from textbooks or articles
- Class lectures covering unique theories or frameworks
- Discussion topics explored during sessions
- Course-specific terminology introduced by instructors
- Proprietary materials not available to external writers
Essays lacking these elements reveal authors unfamiliar with course content. Generic papers applicable to any similar course expose their essay mill origins.
Personal Reflection Errors
Assignments requiring personal experience or reflection create detection opportunities:
- Gender mismatches: A Male student submits an essay referencing “when I was pregnant.”
- Irrelevant experiences: Discussing events the student never participated in
- Geographic inconsistencies: Referencing locations the student never visited
- Timeline contradictions: Describing experiences at times, the student was elsewhere
These errors occur when essay mills recycle content or assign work to writers unfamiliar with student backgrounds.
Suspicious Formatting and Presentation
Technical details sometimes betray purchased origins:
- British spelling in American university submissions (or vice versa)
- Citation styles different from course requirements
- Formatting quirks common to essay mill templates
- Hidden text or white font tricks essay mills use
- Unusual fonts or spacing not matching the student’s typical work
These seemingly minor details accumulate into convincing evidence when combined with other indicators.
Assignment-Specific Weaknesses
Professors increasingly design assignments, making outsourcing difficult:
Process Documentation Requirements
Requiring outline submissions, draft reviews, or progress reports throughout writing. Students must demonstrate ongoing engagement, making the last-minute essay mill use obvious.
In-Class Components
Oral presentations, discussions, or follow-up questions test genuine understanding. Students who can’t discuss their own paper’s arguments expose themselves immediately.
Unique Assignment Elements
Including course-specific data, proprietary case studies, or unusual requirements that essay mills can’t easily fulfill. Generic responses reveal outsourcing.
Trojan Horse Techniques
Some professors embed hidden instructions in white text. When copied into AI prompts, the instructions appear, and AI-generated responses include them. Students who don’t notice submit obvious AI work.
Multiple Submissions of the Same Assignment
When essay mills sell identical or similar papers to multiple students (sometimes at the same institution), Turnitin detects matches between submissions. This instantly exposes cheating and often reveals the essay mill source.
Students who think they’re purchasing “original” work sometimes receive papers previously sold to others. The 42% plagiarism match one student faced came from this exact scenario - the term paper had been sold three times before.
What Are Real Detection Rates?
Understanding actual detection statistics helps assess true risks of using essay services without getting caught.
Professor Suspicion Rates
Research consistently shows high faculty awareness:
- Two-thirds (67%) of academics suspect when submitted work isn’t student-written
- Only half report their suspicions to authorities
- 21.1% of students believe peers frequently purchase essays
- 42.2% suspect peers sometimes commission work
This data reveals a significant gap: many professors detect cheating but don’t always report it. Reasons include:
- Insufficient evidence to prove allegations
- Time-consuming investigation and documentation processes
- Uncertainty about institutional support for academic misconduct cases
- Desire to give students the benefit of doubt on first suspicions
However, detection without reporting doesn’t mean safety. Professors may simply lower grades, provide less favorable recommendations, or watch students more closely on future assignments.
Turnitin Authorship Effectiveness
Controlled studies provide concrete detection rate data:
- 48% baseline detection rate without automated tools (human judgment alone)
- 59% detection rate with Turnitin Authorship Investigation assistance
- 23% improvement in accuracy when combining human expertise with software
- 0.57+ prediction scores flag high-probability contract cheating cases
These numbers reveal important truths. Even sophisticated tools don’t catch everything - 41% of contract cheating potentially goes undetected. However, detection rates continue improving as technology advances and professors receive better training.
AI Content Detection
Turnitin’s AI detection tool data reveals usage patterns:
- 11% of papers contain 20%+ AI-generated content
- 3% consist primarily (80%+) of AI writing
- 68% of teachers now use AI detection tools
However, AI detection faces accuracy challenges. No tool achieves 100% reliability, and false positives occur. OpenAI shut down its own AI detection tool citing high false positive rates for human-written content.
This imperfect detection creates two competing pressures: students may avoid detection while innocent students face false accusations.
Institutional Investigation Rates
Real-world case data shows increasing enforcement:
- One UK university investigated 69 contract cheating cases in 2024, up from five cases in 2022-2023
- Multiple students on single courses caught simultaneously when patterns emerge
- 6% of Australian university students admit to obtaining assignments through third parties
- 31 million students worldwide have used essay services, according to one study
These statistics demonstrate both widespread usage and increasing institutional detection capabilities.
Student Self-Reporting vs. Reality
Discrepancies between admission rates and suspected usage suggest underreporting:
- 3.5% of students admit to buying assignments to submit as their own
- 60% of admitted users did so repeatedly
- 83% of students considered or used essay services
- 67% used services at least once in the past year
The gap between 3.5% admitting to submission as their own versus 67% using services suggests many students either use services as references or underreport direct submission.
Detection Technology Trends
Recent developments indicate accelerating detection capabilities:
- Teacher AI detection tool usage jumped 30 percentage points in one year
- Authorship investigation tools now standard at major universities
- Machine learning continues to improve pattern recognition accuracy
- Cross-institutional databases enable matching across schools
As detection improves, yesterday’s “safe” practices become tomorrow’s obvious cheating. Students who have avoided detection previously face increasing risks as technology advances.
What Happens When You Get Caught?
Consequences extend far beyond failing a single assignment. Getting caught using essay services creates cascading problems affecting academic standing, future opportunities, and personal well-being.
Immediate Academic Penalties
Universities impose progressively severe sanctions:
First Offenses typically result in:
- Zero on assignment - Minimum penalty, losing all points.
- Failing course grade - Entire semester’s work invalidated.
- Academic probation - Restricted status with conditions for continuation.
Serious or Repeat Violations escalate to:
- Suspension - Temporary removal from university (typically one to two semesters).
- Expulsion - Permanent removal with no degree completion.
- Degree revocation - Diplomas rescinded if cheating is discovered post-graduation.
Yale University’s standard cheating penalty is two semesters of suspension, with contract cheating often warranting permanent expulsion. Many institutions follow similar patterns, with purchased essays considered especially egregious violations.
Real Case Examples:
At the University of East Anglia, dozens of economics students faced investigation in 2024 for using essay mills. While not all received maximum penalties, the investigation process itself created significant stress and academic disruption.
Students caught submitting work multiple times face exponentially harsher penalties. What might be probation for a first offense becomes expulsion for repeat violations.
Transcript Notation
Many universities permanently note academic integrity violations on transcripts. These notations remain visible to:
- Graduate schools reviewing applications
- Employers conducting background checks
- Professional licensing boards
- Fellowship and scholarship committees
- Academic honor society membership reviews
Some transcripts note the specific offense (“contract cheating” or “plagiarism”), while others use generic “academic misconduct” language. Either way, the notation creates long-term consequences extending far beyond immediate penalties.
Financial Consequences
Getting caught creates substantial financial losses:
- Scholarship and Aid Termination: Most financial aid requires maintaining academic good standing. Integrity violations often trigger immediate aid suspension or termination, forcing students to repay received funds or find alternative financing.
- Wasted Tuition: Failed courses mean wasted money for that semester’s tuition, housing, and fees. Repeating courses after suspension doubles costs.
- Extended Time to Graduation: Suspension delays graduation by at least one semester, often longer. Additional semesters mean more tuition, housing, and foregone earning potential.
- Lost Services Payment: Money paid to essay services provides no value when caught. There’s no refund policy when academic misconduct is discovered.
One student case revealed $400 per essay payments to essay mills. Multiply that across multiple assignments, add wasted tuition for failed courses, and financial losses escalate rapidly.
Graduate School Impact
Academic misconduct creates major barriers for graduate education:
Application Rejections: Competitive programs eliminate candidates with integrity violations. Why risk admitting someone with proven dishonesty when hundreds of clean candidates apply?
Recommendation Letter Problems: Professors who discover cheating rarely provide strong recommendations. Some refuse entirely. Graduate programs require multiple faculty letters, making this loss devastating.
Personal Statement Difficulties: Many applications ask about academic misconduct. Candidates must explain violations, creating an immediate disadvantage against peers with clean records.
Professional Program Barriers: Medical, law, and other licensed professional programs conduct thorough background checks. Academic misconduct can prevent licensure even after degree completion.
Career and Professional Consequences
Impact extends beyond academia:
Background Check Discoveries: Many employers, particularly in education, finance, government, and healthcare, verify academic records. Misconduct appears during verification, potentially disqualifying candidates.
Professional Licensing Issues: Law, medicine, nursing, accounting, and other licensed professions review character and fitness. Academic integrity violations raise serious questions about professional trustworthiness.
Security Clearance Problems: Government positions requiring clearances investigate academic misconduct as evidence of poor judgment and dishonesty.
Networking and Reputation Damage: Academic and professional communities are smaller than students realize. Word spreads through informal networks about integrity violations, affecting job opportunities and collaborations.
Blackmail and Extortion Risks
Essay mills create unique dangers beyond academic penalties:
Service Provider Blackmail
Essay mills possess permanent evidence of transactions: emails, payments, assignment details, and IP addresses. Unscrupulous operators blackmail students years later, threatening to inform universities or employers unless students pay additional money.
This isn’t hypothetical. Research documents multiple blackmail cases where students paid thousands in extortion after initially paying hundreds for essays. The blackmail can continue indefinitely since services hold permanent evidence.
Payment Disputes
Some students face extortion when payment issues arise. One student’s blackmail began after a payment processing hiccup, with the service threatening university notification.
Privacy Violations
Students share personal information, including names, institutions, courses, and sometimes even student ID numbers. Breaches or malicious use of this data create identity theft and fraud risks.
Recourse Absence
Students have no legal protection. Reporting blackmail to authorities means admitting academic misconduct. The nature of the transaction prevents seeking law enforcement help.
Psychological and Personal Impact
Beyond formal consequences, getting caught creates psychological burdens:
Stress and Anxiety
Investigation processes take weeks or months. Constant worry about outcomes, meeting with administrators, and explaining actions creates intense stress.
Guilt and Shame
Even students who rationalized cheating beforehand often experience significant guilt when confronted. Disappointment from family, friends, and mentors compounds emotional distress.
Self-Efficacy Loss
Getting caught undermines confidence in legitimate abilities. Students question whether they can succeed through honest effort, creating cycles of self-doubt.
Relationship Damage
Family members who invested in education feel betrayed. Friends lose respect. Faculty relationships become adversarial rather than mentoring partnerships.
Imposter Syndrome
Even grades earned honestly afterwards feel tainted. Students wonder if they deserve accomplishments, knowing past success came from cheating.
Depression and Mental Health
The combination of academic crisis, financial stress, future uncertainty, and relationship strain can trigger or exacerbate mental health problems.
Can You Avoid Detection by Modifying Purchased Essays?
Many students believe making changes to purchased work reduces detection risks.
Research and expert analysis reveal this strategy’s limitations.
What Modifications Students Attempt
Common alteration strategies include:
Surface Changes:
- Swapping words for synonyms.
- Rearranging sentence order.
- Changing paragraph sequence.
- Adjusting formatting or citation style.
- Adding or removing sections.
- Rewriting the introduction or conclusion.
Deeper Modifications:
- Incorporating personal examples.
- Adding course-specific references.
- Matching the professor’s stated preferences.
- Simplifying vocabulary to match the typical writing level.
- Introducing deliberate minor errors.
Students hope these changes make purchased work appear authentic. However, these strategies often fail for multiple reasons.
Why Surface Modifications Fail
Authorship Analysis Penetrates Superficial Changes
Stylometric analysis examines deep linguistic patterns unchanged by surface modifications:
- Sentence length distribution patterns
- Function word frequency (the, and, but, with)
- Punctuation usage patterns
- Syntactic structure preferences
- Vocabulary richness measures
These features remain relatively consistent across writing samples but differ significantly between authors. Swapping words or rearranging sentences doesn’t alter these fundamental patterns.
Research shows Turnitin Authorship still flags modified work when underlying patterns differ from the student’s baseline. The 59% detection rate includes attempts at modification - these aren’t just unmodified submissions.
Professor's Notice of Inconsistent Modification
Students who modify work often create new problems:
- Quality Inconsistencies: Professional sections contrast with student-modified parts, creating obvious seams between different quality levels.
- Style Shifts: Different sections show different voices, suggesting multiple authors. Professors notice when introductions sound nothing like body paragraphs.
- Knowledge Gaps: Students modify content about topics they don’t understand, creating nonsensical passages or contradictory arguments.
- Time Stamp Problems: Document metadata may show most content created quickly, then small modifications made just before submission. This pattern reveals purchasing followed by superficial editing.
What Actually Works (And Its Limits)
One real case illustrates partial success:
Courtney, a psychology student, modified her purchased capstone extensively:
- Changed paragraph order
- Deleted the conclusion entirely
- Rewrote the introduction in simpler language
- Made substantial content alterations
She received a B+ and graduated without incident. However, this success required:
- Significant time investment approaching what writing originally would take
- Deep enough understanding to make meaningful changes
- Luck that the professor either didn’t suspect or couldn’t prove concerns
Contrast this with Jamal, who submitted a purchased paper previously sold three times. Turnitin matched 42% of the text to another school’s archive, exposing the cheating immediately.
The difference: Courtney’s essay mill provided truly original content that she extensively modified. Jamal’s was recycled content. But even Courtney took serious risks - many professors would detect the discrepancy between her modified introduction and the professional body paragraphs.
Successful Detection Avoidance Requires Extensive Effort
Students who successfully avoid detection typically:
- Request outlines or rough notes instead of complete essays
- Use purchased work purely as a reference while writing completely original papers
- Spend nearly as much time modifying as writing from scratch would take
- Possess subject knowledge sufficient to make intelligent modifications
- Understand writing well enough to match the purchased content’s sophistication
At this effort level, the question becomes: why not just write the essay yourself? The time, knowledge, and skill required to successfully modify purchased work approach what legitimate writing requires.
Growing Detection Sophistication
As students develop modification techniques, detection methods evolve:
- Machine learning identifies modification patterns
- Comparison algorithms become more sophisticated
- Professor training improves detection of patchwork writing
- Cross-institutional databases reveal recycled, modified content
Yesterday’s successful modification strategies become today’s detected patterns. The arms race continuously favors detection technology over evasion attempts.
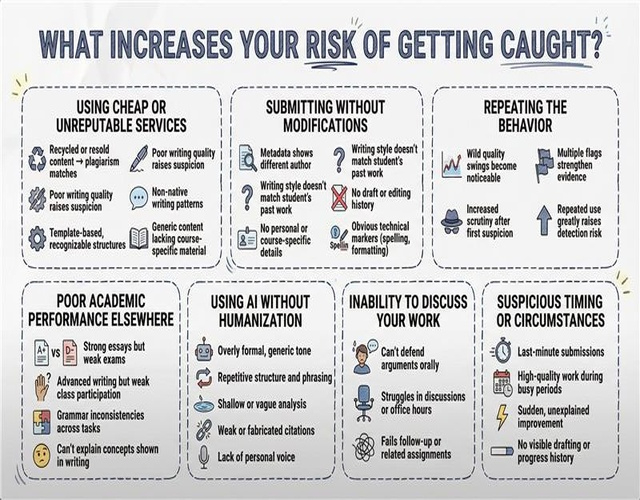
What Increases Your Risk of Getting Caught?
Certain factors dramatically elevate detection probability. Understanding these risks helps students assess true danger levels.
Using Cheap or Unreputable Services
Budget essay mills create multiple detection risks:
- Recycled Content: Cheap services maximize profits by reselling essays to multiple students. Your “custom” paper may have been submitted by students at other institutions, creating obvious plagiarism matches.
- Low-Quality Writing: Poorly written essays with grammar errors, weak arguments, and obvious flaws make professors suspicious. When work quality dramatically exceeds or falls below your typical level, both extremes raise red flags.
- Template-Based Papers: Some services use fill-in-the-blank templates with standard structures and boilerplate content. Professors familiar with these patterns recognize them immediately.
- Non-Native English Writers: Services employing non-native speakers produce writing with characteristic patterns (article usage, preposition choices, idiom avoidance) that differ from native academic English.
- Missing Course-Specific Content: Generic services can’t incorporate specialized course materials, creating obvious knowledge gaps.
Research shows students using cheap services face significantly higher detection rates than those using premium providers. You get what you pay for applies to cheating as much as legitimate purchases.
Submitting Without Modifications
Uploading purchased essays unchanged creates maximum detection risk:
- Document metadata shows authors different from student
- Writing style completely mismatches previous submissions
- Content lacks any course-specific or personal elements
- No progression of drafts or editing history exists
- Technical markers (British spelling, etc.) reveal external origins
Even sophisticated authorship tools aren’t necessary to detect unmodified essays. Basic style comparison reveals the discrepancy.
Repeating the Behavior
Multiple purchases compound detection risks:
- Pattern Recognition: Professors notice when the same student’s writing quality varies wildly across assignments. Exceptional papers alternating with poor work create obvious patterns.
- Statistical Improbability: Multiple authorship flags across different assignments strengthen cases. One suspicious paper might be a coincidence; three or four create compelling evidence.
- Increased Investigation: Professors suspicious of one assignment scrutinize subsequent work more carefully. Once flagged, students face enhanced monitoring, making future cheating detection more likely.
Research shows 60% of students who purchased work once did so repeatedly. This pattern increases cumulative detection probability even if individual instances might avoid notice.
Poor Academic Performance Elsewhere
Quality discrepancies between different assessment types raise suspicions:
- Excellent essays but failing exams on same materia
- Sophisticated written analysis but basic class discussion contributions
- Perfect grammar in papers but error-filled in-class writing
- Complex theoretical understanding in assignments but confusion when explaining concepts
These inconsistencies prompt investigations. Professors cross-reference performance across evaluation types to assess consistency.
Using AI Without Humanization
AI-generated content shows characteristic patterns:
- Overly formal, structured language
- Repetitive sentence structures
- Generic analysis lacking specific insights
- Fabricated or poorly integrated citations Absence of personal voice or unique perspective
Students who submit AI content without extensive humanizing modifications face growing detection risks as 68% of teachers now use detection tools. Even without tools, professors increasingly recognize AI’s distinctive style.
Inability to Discuss Your Work
Professors increasingly require students to explain their arguments:
- Oral presentations defending essay positions
- In-class discussions referencing paper content
- Office hour meetings asking clarifying questions
- Follow-up assignments building on previous work
Students who can’t coherently discuss their own papers expose themselves. This defense requirement makes cheating increasingly risky regardless of detection tool sophistication.
Suspicious Timing or Circumstances
Certain patterns attract attention:
- Last-Minute Submissions: Assignments submitted at the deadline after no prior draft submissions suggest external completion.
- Quality Spikes During Busy Periods: When students submit exceptional work during exam weeks while other assignments suffer, professors question time management.
- Sudden Improvement: Dramatic quality increases between assignments without corresponding knowledge growth in class suggest external help.
- Missing Progressive Development: Assignments requiring draft submissions or progress checkpoints reveal students who suddenly produce complete work without documented development stages.
How Do Professors Confirm Their Suspicions?
When professors suspect essay service usage, they follow systematic investigation processes gathering evidence before making accusations.
Initial Investigation Steps
Review Previous Submissions
Professors compare suspected work against student’s entire submission history:
- Vocabulary comparison identifying unusual word choices
- Sentence complexity analysis measuring structural sophistication
- Argument quality assessment examining analytical depth
- Error pattern analysis checking whether consistent mistakes disappear
- Voice and tone evaluation detecting personality changes
This manual process mirrors what Turnitin Authorship automates. Professors with years of experience develop intuition for detecting style changes.
Verify Citations and Sources
Citation checking reveals multiple red flags:
- Checking whether cited sources actually exist (eliminating AI-generated fabrications)
- Verifying quotes appear in claimed sources
- Confirming sources actually support stated arguments
- Identifying suspicious citation formatting patterns
- Detecting reference lists reused from essay mills
Many professors randomly verify several citations. If sources don’t exist or contain different content than cited, it confirms suspicions.
Consult with Colleagues
Professors share concerns with:
- Other instructors who taught the student in previous courses
- Teaching assistants familiar with student’s work
- Department colleagues experienced in detecting cheating
- Academic integrity officers providing institutional guidance
Colleagues may reveal similar suspicions about the same student or provide additional context about the student’s typical work quality.
Run Detection Software
After initial suspicion, professors deploy available tools:
- Turnitin Similarity Report checking text matches
- Authorship Investigation comparing stylometric patterns
- AI Detection analyzing content for AI-generation likelihood
- Metadata examination reviewing document properties
These tools provide objective data supporting or refuting suspicions. However, lack of software evidence doesn’t eliminate concerns - professors may proceed based on other factors.
Confirmation Methods
Request Draft Submissions
When suspicious, professors may:
- Require draft submissions for future assignments
- Request outlines showing progressive development
- Mandate progress check-ins throughout writing process
- Ask for research notes and source selection justification
Inability to produce drafts or intermediate work strengthens cheating allegations. Legitimate students easily provide progressive development evidence.
Conduct Oral Examinations
Many institutions now require students to defend written work orally:
- Explain main arguments and supporting evidence
- Discuss research process and source selection
- Defend positions against counterarguments
- Clarify specific passages or claims
Students who wrote their own work answer confidently. Those who purchased essays struggle explaining arguments they didn’t develop, discussing sources they didn’t read, or defending positions they don’t understand.
Compare In-Class Writing
Professors may:
- Assign in-class essay on related topic
- Compare handwritten work to typed submissions
- Note vocabulary and complexity differences
- Assess whether student can replicate submitted work’s quality
Dramatic differences between supervised and unsupervised writing confirm outsourcing suspicions.
Review Authorship Reports
Turnitin Authorship provides dashboards showing:
- Prediction scores flagging likely contract cheating
- Flag summaries highlighting concerning patterns
- Document comparison charts showing style variations
- Metadata inconsistencies across submissions
Professors review these reports systematically, documenting evidence for potential academic misconduct proceedings.
Investigation Documentation
Throughout investigations, professors carefully document:
- Initial suspicion triggers and specific concerns
- Comparison data between suspicious and previous work
- Software tool results and interpretation
- Student interactions and explanations
- Colleague consultations and recommendations
- Timeline of evidence gathering
This documentation supports formal misconduct allegations if professors decide to pursue discipline. Without sufficient evidence, most professors don’t proceed - explaining why only half of suspicious instances get reported despite two-thirds being detected.
Confronting Students
When evidence seems compelling, professors typically:
Schedule Private Meetings
Initial conversations happen privately, allowing students to:
- Explain apparent discrepancies
- Provide evidence of legitimate work
- Admit to violations if guilty
- Understand allegations and potential consequences
Some students admit cheating during these conversations, simplifying the process. Others provide legitimate explanations for suspicious patterns.
Present Evidence
Professors share specific concerns:
- Style comparison examples showing differences
- Citation verification results revealing problems
- Software reports highlighting red flags
- Performance inconsistency data across evaluations
Concrete evidence makes allegations harder to deny than vague suspicions.
Offer Opportunities for Defense
Students can provide:
- Draft documentation proving progressive development
- Research notes showing legitimate work process
- Explanations for style changes (tutoring, improved skills)
- Evidence addressing each specific concern
Legitimate students typically address concerns satisfactorily. Those who cheated struggle explaining objective evidence.
Formal Proceedings
If professors conclude cheating occurred based on evidence, cases proceed to:
- Department chairs or academic deans
- Academic integrity committees Student conduct boards
- University disciplinary processes
These formal proceedings follow institutional policies, with students having rights to representation, evidence review, and appeals. However, compelling evidence makes a successful defense difficult.
Key Takeaways: Understanding Your Detection Risk
Getting caught using essay services is a real and increasing risk. Technology, training, and institutional commitment to academic integrity combine to expose contract cheating more effectively than ever before.
Critical points to remember:
- Detection methods are sophisticated and multi-layered. Universities employ writing style analysis, Turnitin Authorship Investigation, AI detection tools, citation verification, and professor expertise. Research shows 59% detection rates with modern tools, with accuracy continuously improving as technology advances.
- Two-thirds of professors suspect when work isn’t student-written, even if only half formally report suspicions. This means many students avoid punishment but not detection. Professors may simply lower grades, provide poor recommendations, or watch subsequent work more closely.
- Consequences extend far beyond failing assignments. Getting caught risks suspension or expulsion, permanent transcript notation, scholarship loss, graduate school rejection, career barriers, and blackmail from essay services. One UK university alone investigated 69 cases in 2024, up from five the previous year.
- Modifications don’t reliably prevent detection. Surface changes like synonym swapping don’t fool stylometric analysis. Meaningful modifications require time and knowledge approaching what original writing would take, defeating the purpose of purchasing work.
- Cheap or repeated usage dramatically increases risks. Low-quality services often recycle content, creating obvious plagiarism matches. Multiple purchases create patterns professors recognize. Budget services employ non-native writers whose characteristic patterns professors identify.
The uncomfortable truth: If you spend enough time and possess sufficient knowledge to successfully modify purchased work avoiding detection, you could write the essay yourself in similar time. The effort required for successful cheating approaches legitimate work effort - without the learning, skill development, or peace of mind.
Make the Smart Choice for Your Academic Future
Understanding detection methods and consequences empowers better decisions. The question isn’t just “Can I get caught?” but “What are the long-term costs even if I don’t get caught?”
Skills developed through genuine effort create lasting value. Writing, research, and critical thinking abilities serve your entire career. Professional essay writing services can support learning when used as reference materials, but submission as your own work carries risks far outweighing temporary grade benefits.
Consider legitimate alternatives: university writing centers, professor office hours, tutoring services, time management improvement, and honest conversations about workload challenges. These options provide real support without jeopardizing your academic future.
Your education is an investment in capabilities that will serve you throughout life. Protect that investment by maintaining integrity. Visit our trusted essay writing service to learn how professional support can enhance rather than replace your learning journey - ethically and safely.
The temporary relief of outsourcing work isn’t worth permanent consequences. Choose integrity. Choose learning. Choose to invest in skills that will genuinely serve your future.
-18298.png)



